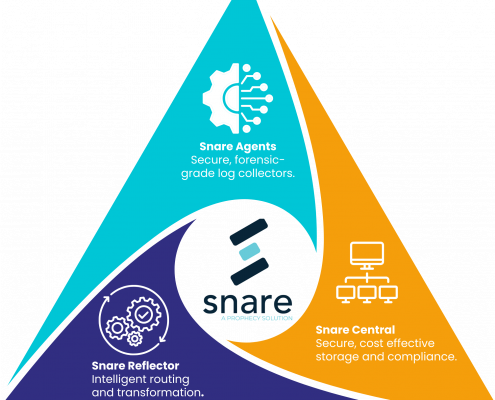
Snare Agent
Enterprise-Grade Log Collection That’s Secure, Scalable, and Smart
Snare Agent is the industry’s most trusted endpoint log collector, engineered to deliver tamper-resistant, high-fidelity logs from across your IT estate — whether you’re operating in Windows, Linux, MacOS, or cloud environments.
From compliance and threat detection to long-term log storage and SIEM optimization, Snare Agent is your lightweight, low-latency solution for precise, secure log collection — at scale.