Achieve Compliance Without SIEM Fees
Meet Regulatory Requirements While Controlling Your Costs
Unlock Compliance. Cut the Costs.
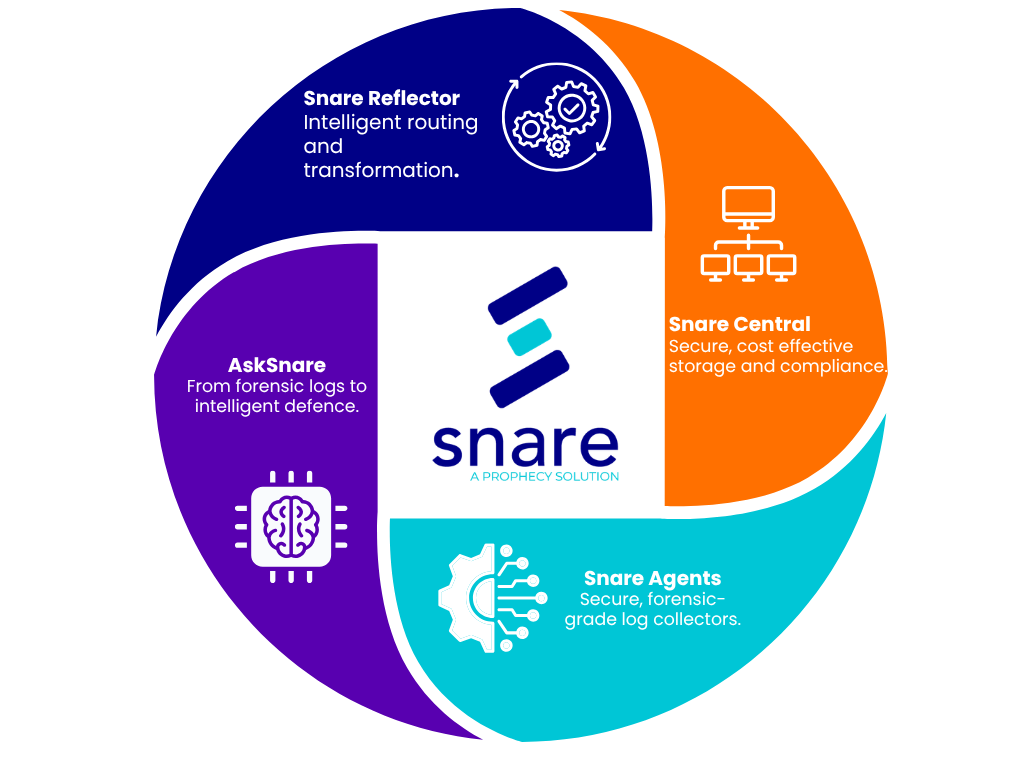
Snare reduces SIEM costs by collecting high-fidelity logs at the source, applying advanced filtering and compression, and routing only relevant events to SIEM platforms. This lowers ingestion volume and storage requirements while preserving forensic-quality logs for investigations, compliance, and replay when full detail is required.