Background on the Print Spooler Vulnerability
The recent threat posted by Microsoft for a print spooler vulnerability is subject to exploitation from tools such as Mimikatz, a tool that can steal user credentials and potentially facilitates lateral movement of an attacker in the network.
PrintNightmare directly affects the native Windows service named “Print Spooler” that is enabled by default on Windows machines. The purpose of Print Spooler is to manage printers and printer servers.
This covers the remote code exploitation of systems from the vulnerability. As of the 2nd of July, Microsoft has not fully patched the problem and still rates it as critical. Microsoft has published some workarounds to allow customers to potentially avoid the issue by reducing services/capabilities.
The process of exploiting the vulnerability will generate several print spooler events (event ID 316) in the PrintService-Operational custom windows event log.
How Snare Can Help
The Snare Enterprise Windows agents will collect any custom Windows event logs, that have been enabled by the administrator out of the box. The generation of PrintService custom logs can easily be enabled from either the Windows event viewer or from the group policy setting, at which time they will be picked up by the Snare agent and forwarded to your collection target system.
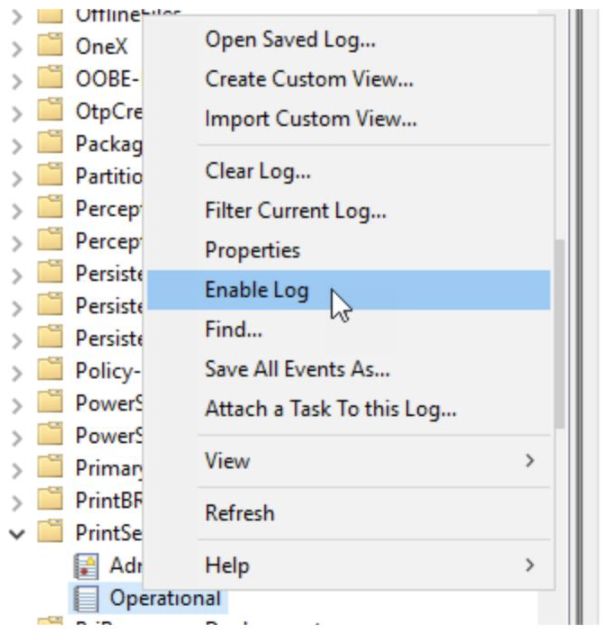
Open the Windows Event Viewer application then navigate to the Application and Service Logs → Microsoft → Windows → Then scroll down to PrintService and expand to see the Operational log then right click to enable.
An example as follows:
Once enabled, logs will appear in this log and the Snare Agent will collect and send the logs to the Snare Central or your other target SIEM system.
In Snare Central, a specific report can be created for these events and a real-time alert can be triggered when one or more target events appear over a designated timeframe.
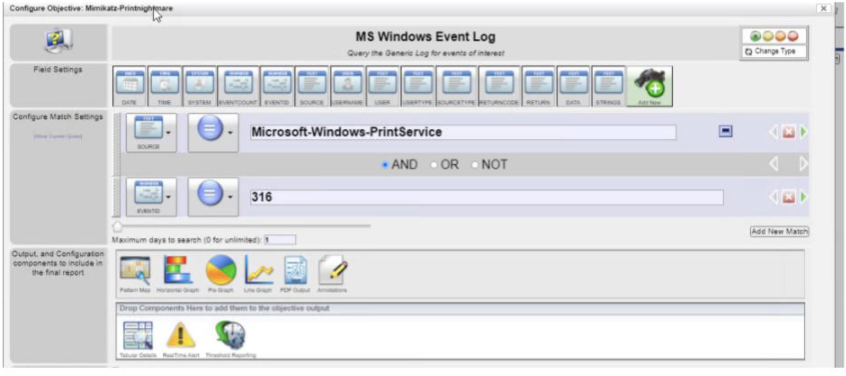
Create a new report using the menu using the “Add new objective” button in a report container of choice.
Change the log type to MS Windows Event Log – Adhoc query
An example of a report is provided below.
The source type has been configured with the name of the custom event log, the eventid has been set to 316 and the number of days set to 1 in order to limit the report to the most recent data. This can be adjusted to search for more days as needed:
To display the events that meet these requirements, adjust the tabular reporting to show the following fields.

Adjust the number of rows and pages to suit the number of rows being generated, keep in mind the larger the output the longer the report may take to generate.
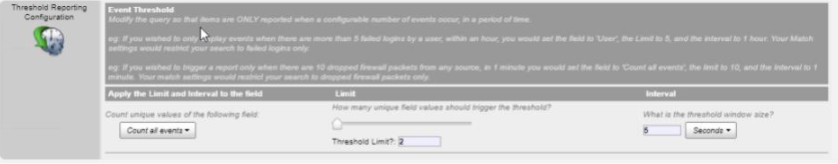
For real time alerting based on a threshold of 2 events in 5 seconds you can set the criteria as follows:
Select “Set” to save the report. Now set the schedule to provide the email address for the alerts to go to.
This will use the SMTP gateway as set in the configuration Wizard.
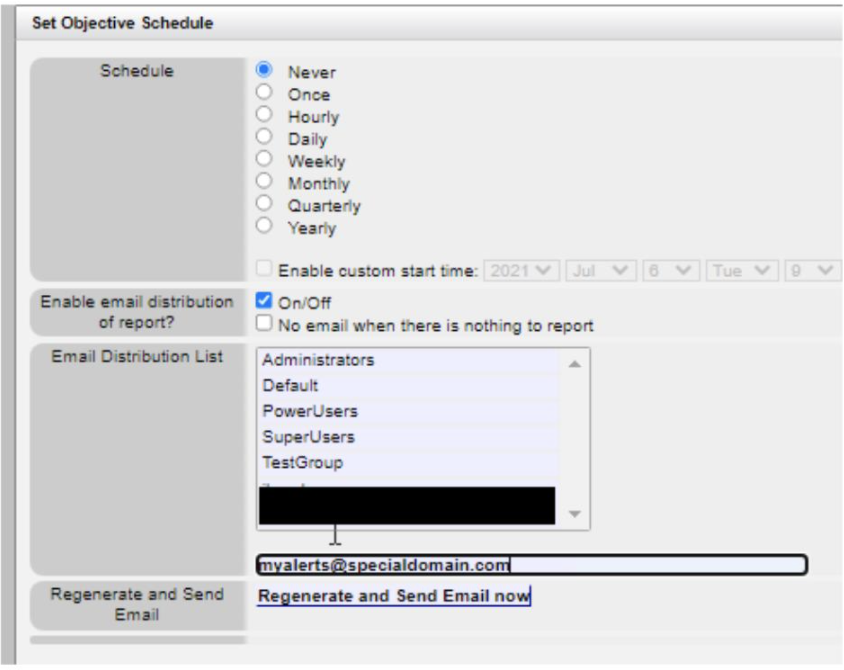
Once active, if any “316” eventIDs in the PrintService event log are received, a real-time alert will be generated.
Need help from Snare’s Team?
Contact our team if you have questions about the PrintNightmare incident or how to set up Snare to manage or audit printer server logs.

